January 12, 2026
Right now, millions are embracing Dry January.
They're giving up their unhealthy fix not just to feel better, but to boost productivity and stop postponing change with "I'll start Monday."
Your company has its own "Dry January" list—except it's filled with damaging tech habits, not cocktails.
These are the risky, inefficient routines everyone knows they shouldn't do, yet keep justifying with "it's fine" or "we're busy."
Until suddenly, it's not fine anymore.
Here are six harmful tech habits to absolutely quit this month, along with smarter alternatives.
Habit #1: Postponing Software Updates with "Remind Me Later"
This tiny button has endangered more small businesses than any hacker.
We understand no one wants an unexpected restart mid-day. But updates aren't just feature add-ons—they patch critical security flaws hackers are actively targeting.
Delaying updates turns "later" into weeks, then months, leaving your software vulnerable to cybercriminals.
Remember the devastating WannaCry ransomware? It wreaked havoc worldwide by exploiting a vulnerability patched months earlier—yet countless victims had ignored update prompts.
The fallout: billions lost across 150+ countries as operations ground to a halt.
Break the habit: Schedule updates for the day's end or let your IT team install them silently in the background—zero disruptions, zero risk.
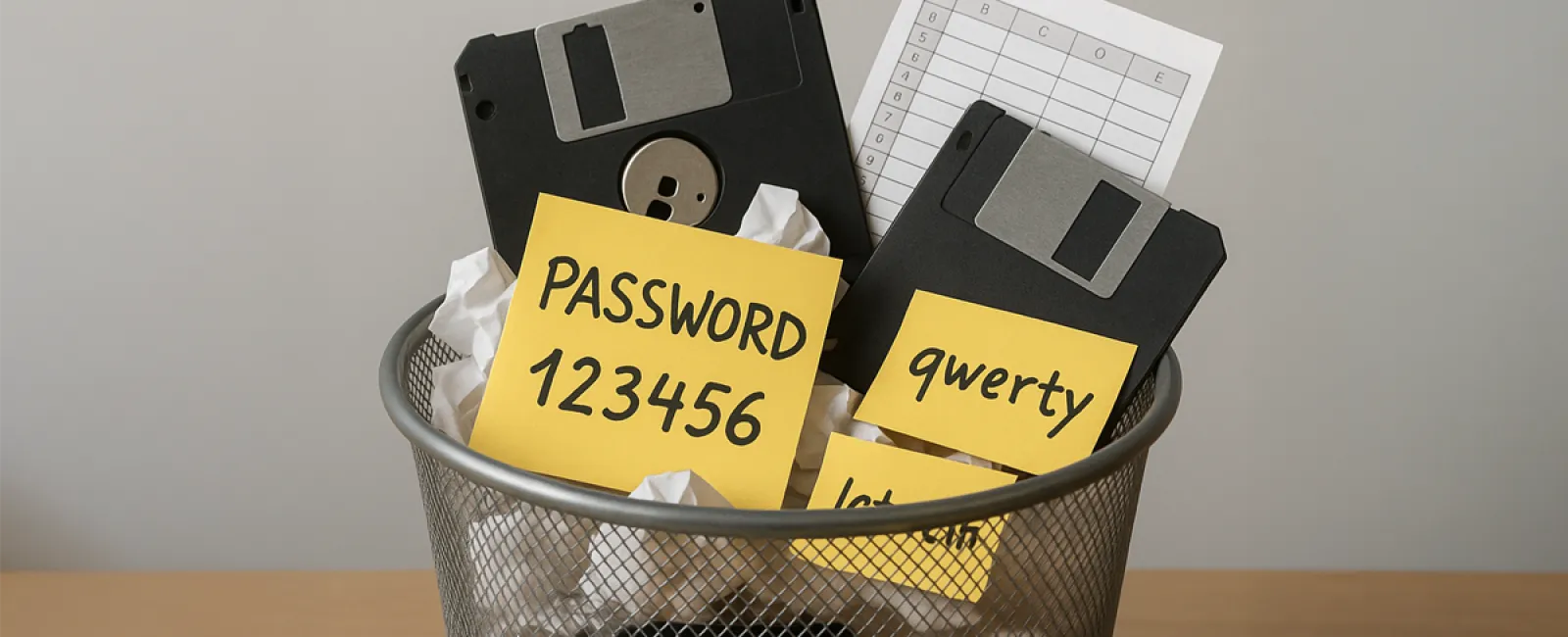
Habit #2: Using One Password for Everything
Everyone has that go-to password.
It feels strong, meets all criteria, and it's easy to recall. So you use it everywhere—from email and banking to online shops and forgotten forums.
Here's the catch: Data breaches happen constantly. That obscure forum leaked your credentials last year, now circulating on dark web marketplaces.
Hackers don't need to guess your passwords—they already have them. They try breaches everywhere, opening doors where your reused password works.
This attack, known as credential stuffing, causes numerous account compromises. Your "strong" password? It's a stolen master key.
Break the habit: Adopt a trusted password manager like LastPass, 1Password, or Bitwarden. Use one master password while the tool creates and remembers complex, unique passwords for every site. Setup takes minutes; security lasts forever.
Habit #3: Sharing Passwords via Email or Text
"Can you send the shared account login?"
"Sure! admin@company.com, password Summer2024!"
Sent over Slack, text, or email—quick fix in 30 seconds.
Only problem? That message is permanently archived.
Stored in sent folders, inboxes, cloud backups, searchable and forwardable. One compromised email account is all a hacker needs to grab every shared credential.
It's like mailing your house keys on a postcard.
Break the habit: Use password managers with secure sharing features. They grant access without revealing the password and can be revoked anytime—no trace left in emails. If you must share manually, split credentials across different channels and immediately reset the password afterward.
Habit #4: Granting Everyone Admin Rights for Convenience
Someone needed to install software or tweak settings, so instead of assigning specific permissions, you made them admin.
Now half your team has full admin access simply because it's easier.
Admin access allows installing software, disabling security, changing critical settings, or deleting files—and if those credentials are compromised, attackers inherit full control.
Ransomware thrives on such broad access. More permissions mean more damage, faster.
Handing out admin rights like candy is like giving everyone keys to the safe for a stapler.
Break the habit: Follow the principle of least privilege: everyone gets exactly the access they need and nothing more. Yes, setting this up takes a bit longer, but it's a small price compared to the havoc a breach or accidental deletion can cause.
Habit #5: Letting "Temporary" Workarounds Become Permanent
Something broke. You found a quick fix. "We'll do it right later."
Years pass.
That workaround becomes the standard procedure.
Maybe it adds extra steps or relies on someone remembering a trick—but it works, so why fix what's "not broken"?
In truth, these extra steps drain productivity multiplied across everyone, every day.
Worse, workarounds create fragility: they depend on specific conditions and knowledge. When changes occur, the whole process can collapse with no clear fix.
Break the habit: Compile a list of workarounds used in your business. Don't try to fix them alone—you'd have done so already if it were easy. Instead, let us help you replace these fragile band-aids with reliable, efficient solutions that save time and frustration.
Habit #6: Relying on a Single Spreadsheet to Run Your Business
You know the one:
An Excel file with a dozen confusing tabs and complex formulas no one fully understands. Only a few people know how it works, and the original creator is gone.
If it gets corrupted, what's your backup? If those who understand quit, who will maintain it?
That spreadsheet is a ticking time bomb disguised as a business tool.
Spreadsheets lack audit trails, aren't scalable, don't integrate with other software, and often aren't backed up properly. You've built critical systems on fragile digital duct tape.
Break the habit: Document the business processes your spreadsheets support, not just the file. Then seek purpose-built tools: CRM software for customers, inventory systems for stock, scheduling apps for appointments. These solutions offer backups, permissions, and audit trails—unlike fragile spreadsheets. Remember, spreadsheets are excellent for data manipulation—not foundational systems.
Why These Tech Habits Are So Hard to Break
You already know these aren't good choices.
It's not ignorance—it's the relentless pace of business.
These bad habits persist because:
- The negative outcomes stay hidden until disaster strikes. Password reuse feels harmless until it triggers a massive breach.
- The "correct" actions seem slower upfront. Setting up a password manager takes time, but typing an easy password feels faster—until the breach happens.
- Everyone else is doing the same. Sharing passwords on Slack feels normal, so risks get ignored.
This mirrors why Dry January helps even the most willful change-makers: it forces awareness, interrupts autopilot, and reveals invisible risks.
How to Kick These Habits Without Relying on Willpower
Willpower alone won't win Dry January—environment does.
And it's the same with tech habits.
Companies that break bad tech routines don't just try harder—they alter systems so the right way is effortless:
- Password managers rolled out company-wide remove the temptation to share passwords insecurely.
- Automatic updates eliminate the "remind me later" delay.
- Centralized permission controls keep admin access from being everyone's default.
- Workarounds get replaced with dependable solutions built to last.
- Critical spreadsheets migrate to robust systems with backups and secure access.
When the easy choice is the right choice, bad habits fade away.
That's what a proactive IT partner does: not preach, but transform your tech landscape so the smart behavior is the natural default.
Ready to Break the Tech Habits Quietly Holding Your Business Back?
Schedule your Bad Habit Audit today.
In just 15 minutes, we'll explore your business's unique challenges and provide a clear action plan to permanently fix them.
No lecture. No confusing jargon. Just a streamlined, secure, and more profitable 2026.
Click here or give us a call at 905-947-1636 to book your 15-Minute Discovery Call.
Because some habits deserve to be quit cold turkey—there's no better time than January.